
2025 ended with 386.9 million domain name registrations across all top-level domains (TLDs), an increase of 22.7 million, or 6.2%, year over year, according to the latest Verisign Domain Name Industry Brief released Thursday.
Global Domain Name and Internet Policy News

2025 ended with 386.9 million domain name registrations across all top-level domains (TLDs), an increase of 22.7 million, or 6.2%, year over year, according to the latest Verisign Domain Name Industry Brief released Thursday.

tldbox GmbH has announced its successful evaluation as a Registry Service Provider (RSP) under ICANN’s upcoming New Generic Top-Level Domain (gTLD) Program.

Switzerland’s ccTLD .ch will continue to be managed by Switch for five more years from January 2027, the country’s Federal Office of Communications (OFCOM) announced last week, with the option of extending for another five years.
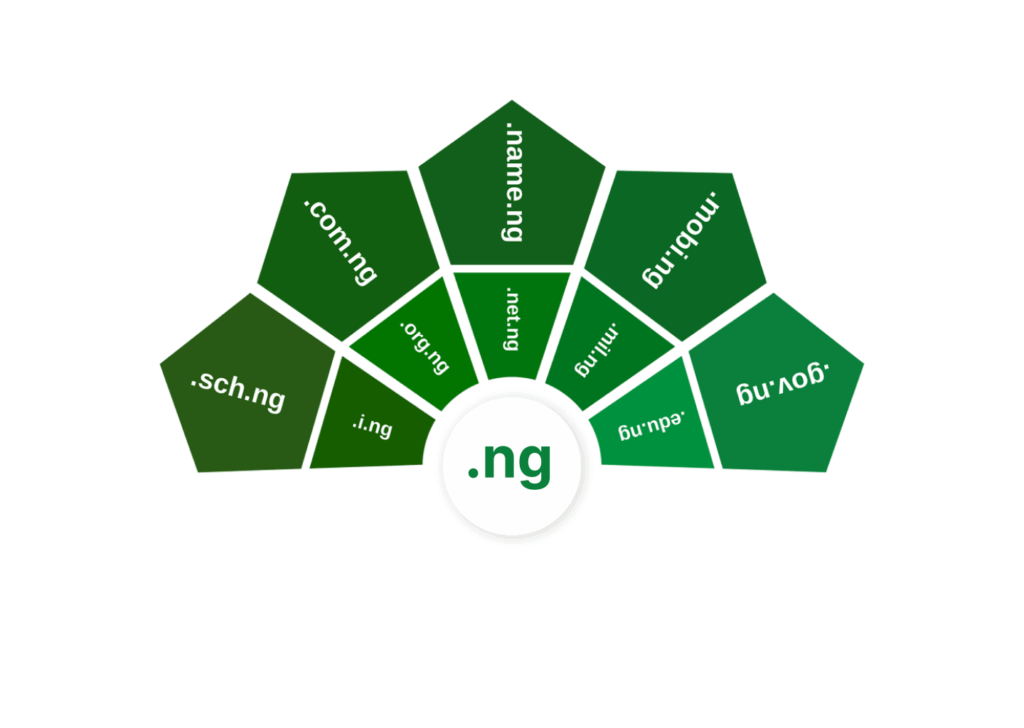
The Nigerian Senate, a number of government agencies and industry have all called for Nigerians to increase their use of the country’s ccTLD .ng at the recent Tech Convergence 2.0 event, organised by the Nigeria Internet Registration Association (NiRA).

As usual, ICANN’s annual general meeting in Dublin last week saw plenty of resolutions approved including the reappointment of Tripti Sinha as chair and appointment of Sajid Rahman was, somewhat controversially, appointed as Vice Chair; continue operations of the Whois successor the Registration Data Request Service for another two years; approved the New gTLD Program: 2026 Round Applicant Guidebook, three future meetings in Muscat, Seville and Vancouver and more.
Continue reading “ICANN Dublin Approves New gTLD Guidebook, 3 Meeting Locations, RDRS Continuance, Sinha Reappointed Chair, Rahman New Vice-Chair”
The annual .ORG Impact Awards winners were announced recently with the top award, the ORG of the Year, being awarded to Fonds pour les Femmes Congolaises (The Fund for Congolese Women) along with a US$50,000 donation from award organisers Public Interest Registry.

A year of change at the top of the German-speaking ccTLD registries has culminated with Thomas Sutter being elected as the new Managing Director of the Switch Foundation, which has the responsibility for operating the registries for .ch (Switzerland) and .li (Liechtenstein).
Continue reading “Thomas Sutter Elected As New Managing Director of Switch”
The Public Interest Registry (PIR) unveiled the finalists for the 2025 .ORG Impact Awards Tuesday and announced rapper, philanthropist and activist Common will host this year’s awards ceremony in Washington, D.C. in October that will recognise outstanding mission-driven individuals and organisations from around the world for their positive contributions to society.

Registrants of .org domain names have one more week to nominate for the 2025 edition of the .ORG Impact Awards, awards that recognise some of the best websites and organisations behind .org domain names.

ICANN published its tax returns for itself and its affiliate Public Technical Identifiers for the year ending 30 June 2024 this week. When combined with looking at the corresponding annual reports, they show soaring expenditures but income has plateaued. While ICANN attributes some of the increased expenditure to the upcoming new gTLD expansion, what does this mean for registries, registrars and registrants? Higher prices?